WordPress Two Factor Authentication Core Files post talks about security and two factor implementation for your website.
Last Updated: December 4, 2024
Latest News: I updated the information below.

WordPress are going in the right direction. They have decided to implement better security into the core file system. This will help fight brute force login attempts and stolen passwords. This new security feature might not be added to the core files. You can read more about it from the following URL the-two-factor-plugin-is-currently-on-a.
What does this means for many of you running WordPress? You won’t have to install a Two Factor plugin any more if you had one installed unless you prefer and like the plugin you are using. It also means that it will be extremely challenging for hackers to brute force attack into your website.
Note: You might also be interested in reading the following tutorial Google Authenticator Security WordPress.
Two Factor version 0.10.0 changelog. Check the following URL two-factor releases to learn more about the changelog.
What You Need:
WordPress Two Factor Authentication Core Files
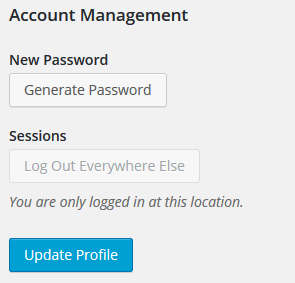
Step 1 ) The following image shows you the standard WordPress profile before you activate the plugin.
Step 2 ) Once you activate the plugin you will see the following settings in your profile.
Two-Factor Options Part 1
- Email – Authentication codes will be sent to your email address.
- Time Based One-Time Password (TOTP)
- Authentication Code:
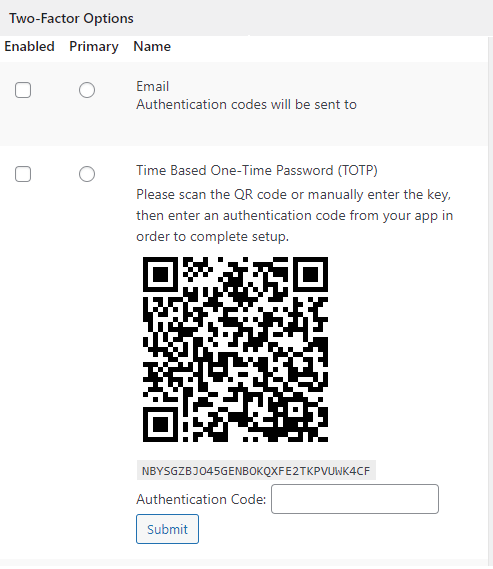
Step 2-a ) The following image allows you to select from the following options.
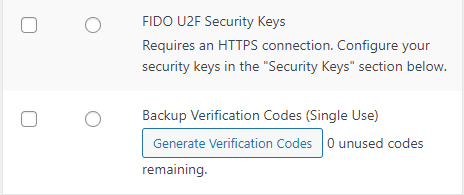
Two-Factor Options Part 2
- FIDO U2F Security Keys
- Backup Verification Codes (Single Use) Click on Generate Verification Codes button 0 unused codes remaining.
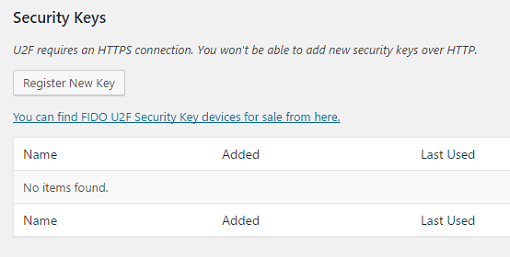
Step 3 ) The following image Security Keys allows you to generate security keys if you selected this option in Step 2-a ) above.
Note: U2F requires an HTTPS connection. You won’t be able to add new security keys over HTTP.
You can see how much security this new feature will add to WordPress once it is implemented. I know all of you will be very happy once it is out.
I will be updating this tutorial from time to time so keep coming back for the latest updates.
If you have a questions send me an e-mail or leave a comment.
Enjoy.